This post should be called Hacking WCF as I will show some configuration hacks in WCF. Read part 2 here where I discussed the clientaccesspolicy.xml and crossdomain.xml files.
This post should be called Hacking WCF as I will show some configuration hacks in WCF. Read part 2 here where I discussed the clientaccesspolicy.xml and crossdomain.xml files.
The Csla WcfPortal I discovered in part 1 (here) is my next subject. A WCF service can expose meta information to generate a proxy for access from code. The meta information is requested by adding the ?wsdl query to the service endpoint. An example: http://www.restfulwebservices.net/wcf/CurrencyService.svc?wsdl.
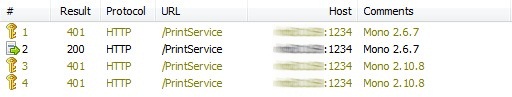
Fortunate for me the meta information is exposed. Now I can generate a proxy and use it in a console application. Gotta love the commandline 🙂 The first call gives and exception about the security settings. The response hands me a list of allowed security settings. After adding credentials (which I was given) my application can read records from the WcfPortal. I am in.
Why was the meta information exposed? The information is not needed for normal operation. Probably a developer forgot to turn the setting off in the web.config.
Now the fun part starts. Getting the WcfPortal to give me information it should not give by experimenting with the parameters. Every exception thrown inside the service is send back to my hacking application. Now I get a good sense of what is happening in the service.
Why are the exception details send back to my application? Again a setting in the web.config that should be changed.
<configuration>
<system.serviceModel>
<!-- Other stuff removed for clearity -->
<behaviors>
<serviceBehaviors>
<behavior>
<!-- set httpGetEnabled to false to stop exposing meta information -->
<serviceMetadata httpGetEnabled="false" />
<!-- set includeExceptionDetailInFaults to false to stop exposing exception details -->
<serviceDebug includeExceptionDetailInFaults="false" />
</behavior>
</serviceBehaviors>
</behaviors>
</system.serviceModel>
</configuration>
In regard to the previous findings I rate these settings a higher security risk. They expose information you don’t want to expose and can even be seen as an open invitation to get hacked. The effort to change these two settings is nothing compared to the damage they could cause.