Lately I noticed my Windows 8.1 machine was taking a long time to become responsive after login. The files in Explorer would only show up after a terrible long load, and the icons would still be white. After some time (too long) everything was responsive again and my work could start.
Today I used the Windows Performance Toolkit and MagicAndre1981‘s post as a guide. After the first reboot and generating the summary the search for my waiting started.
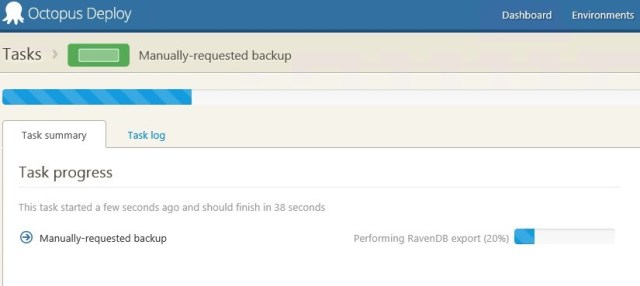
Somewhere at the lower end of the summary file I found ServiceControl and RavenDB to be taking a lot of time.
<serviceTransition name="Particular.ServiceControl"
processingTimeDelta="72962"
container="ServiceControl.exe (2188)"/>
<!-- removed other items and details -->
<serviceTransition name="RavenDB"
processingTimeDelta="20043"
container="Raven.Server.exe (2420)"/>
Both items are services and set to start automatic on boot. By setting the start option to Automatic (Delayed start) I can breath again. The services do start, but 2 minutes after the last automatic service has started.
Problem solved.